Update 2020-06-03: It’s been a long time since I first posted this. It’s quite possible these problems are all fixed. I haven’t tested—sorry!
Update 2017-11-03: Some of these issues have been improved on macOS Safari (I didn’t check iOS). Original post follows.
Last week I filed three bugs with Apple regarding how Safari handles invalid certificates.
Bug #1 (Mac OS and iOS): It’s way too easy for a user to bypass a certificate warning. There’s a bunch of text no one will read and a big friendly “Continue” button. Invalid certificates are serious and should not be ignored lightly. Your average user doesn’t know this. It’s the responsibility of the browser to treat invalid certificates with appropriate gravitas. Safari fails here.
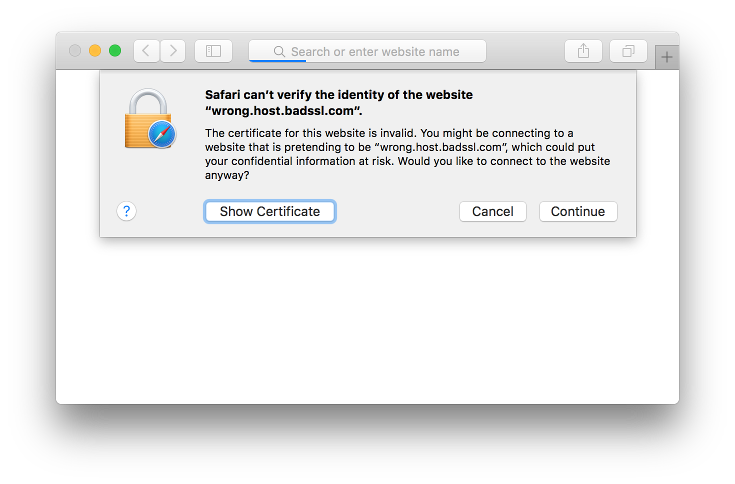
Screenshot of Safari’s invalid certificate warning on Mac OS
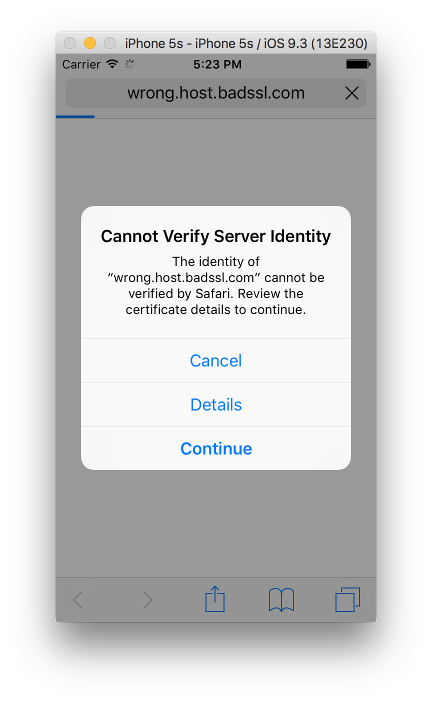
Screenshot of Safari’s invalid certificate warning on iOS
Bug #2 (iOS): After continuing through a certificate warning, the address bar displays a closed padlock icon. This falsely indicates to the user that their interactions with the page are secure.

Screenshot of Safari after continuing through an invalid certificate warning
Bug #3 (iOS): If a user continues through a certificate warning, this decision should expire at some point. Maybe if the user visits the site in a new browser window. Maybe after a certain amount of time has gone by. As far as I can tell the cert bypass is remembered indefinitely.
Combined, these three issues greatly undermine the effectiveness of https on iOS. I’d wager that it’s significantly easier to perform a man-in-the-middle attack of an https site on an iOS Safari user than an iOS Chrome user.
Apple: You’re one of the biggest companies in the world. You command huge shares of the consumer computer and mobile device markets. Fix your shit.

Warning, shameless self promotion. We think cert exceptions should expire after 1 week: https://joelweinberger.us/papers/2016/weinberger-felt.pdf
Joel: That’s great info, thanks for sharing (and doing tons of research and writing a great paper and sharing publicly). One week sounds like a great choice to me.